Why create a pentest lab?
Installing various tools such as nmap and metaspoilt can be messy and you miss out on all the work that has gone into Kali Linux, the gold standard of Pentesting. Most commonly, you will end up having a Kali Linux VM as your pentest environment and use it to sacn/test/attack targets. This in itself has risks in that anauthorised access to machines is illegal (Computer Misuse Act in the UK) and there are cases where simple scanning ended up in a criminal conviction, such as a 17 year old in Finland who in 2003 was convicted for scanning network ports. . This nmap page on legal issues gives a good overview of the risks
Unless therefore you are testing systems that a client or emprloyer has auhorized you (in writting) to do, you want to restrict your learning on systems on your macine, by using Virtual Machines. Whilst you are learning, you want those tools isolated from the external world so that you can avoid accidental harmful acts such as causing by accident a denial of service attack.
Finally, intenionally insecure Virtual Machines offer a good foundation to learn and experiment with known vulnerabilities without looking for needles in a haystack or risking exposing existing systems. We use metasploitable, a popular intentionally vulnerable VM but there are others you can add later on, from sites such as vulnerable hosts.
The Cyberia PenTest Lab
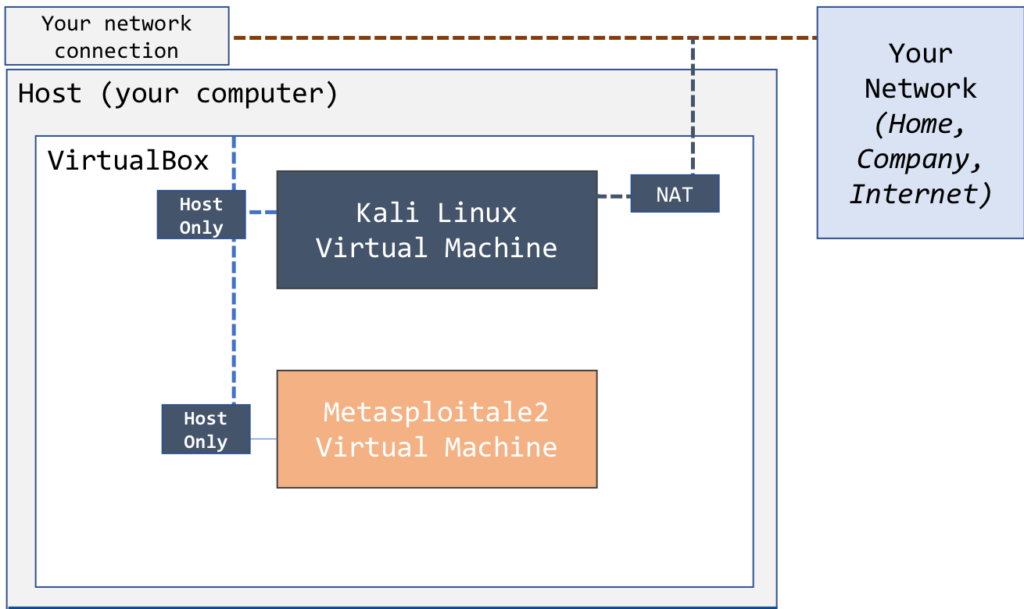
The Cyberia Pentest Lab is the simplest possible lab of virtual machines
It creates a basic network on the host machine (your laptop or desktop) wihih isolated from the external work but also provies a connection to the outside wold for updates etc with the option to disable the external link from within Kali.
Install Virtual Box
There are no really many reasons to chose between VMWare and Virtual Box other than the fact that VirtualBox is free on all three platforms (Windows, Mac, Linux) whereas VMWare is not not free on Mac (VMWare Fusion). Having said that, if you are a student, check with your institution whether they may provide free VMware licences.
Regardless of licencing considerations, VirtualBox is an excellent virtualisation product and free to use. To insatl
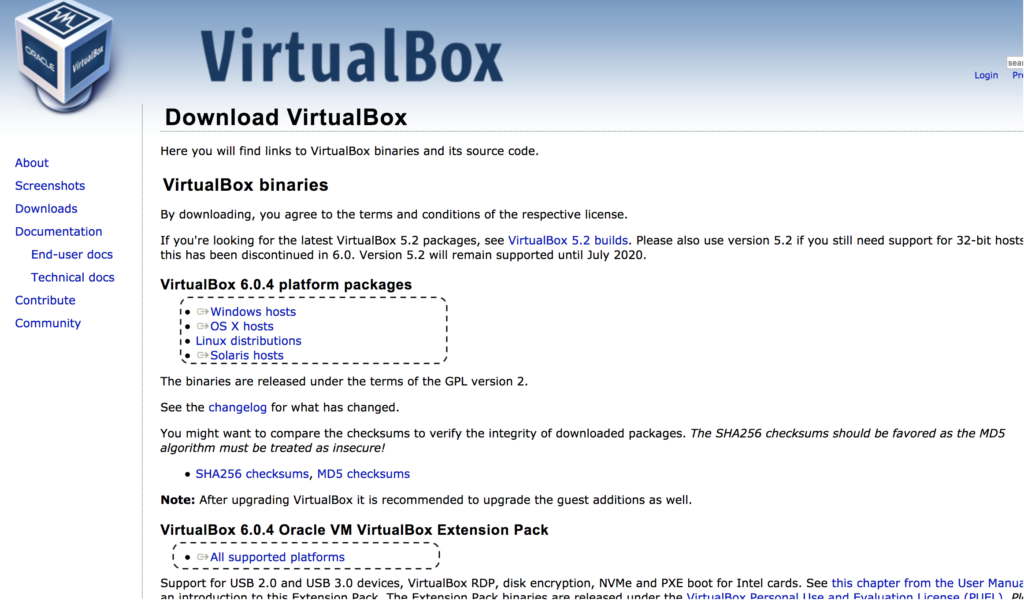
https://www.virtualbox.org/wiki/Downloads
Click on the OS matching your host and download the installer.
Also click and download the VirtualBox Oracle VM VirtualBox Extension Pack. Ths will eliminate maby errors in importing and/or running the Kali Linux (incl the ones related to USB ports)
Once the two files are downloaded, double click and run the installers, starting with the VirtualBox Installer first.
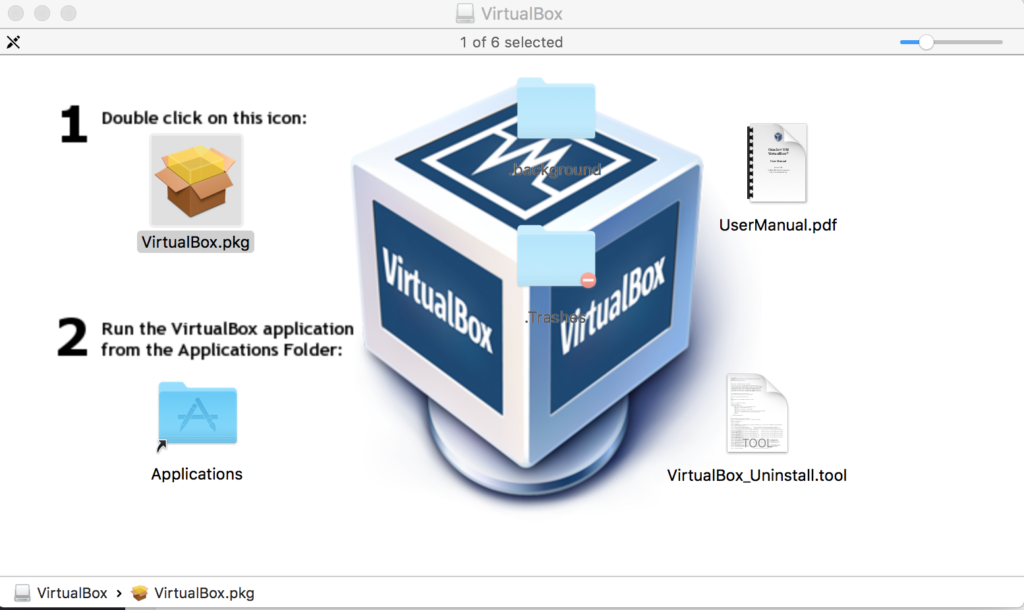
Mac users will see this and need to double click and run the VirtualBox.pkg and once installed find and run the VirtualBox.app in their Applications folder
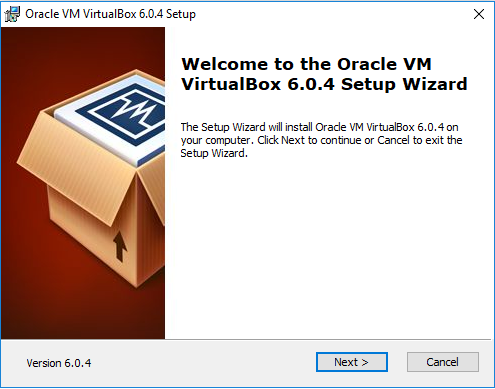
Windows users will see the VM Wizard. Click next on all prompts and finish the installation, which will then run VirtualBox.
Linux users will run the installer of their distribution by opening the file.
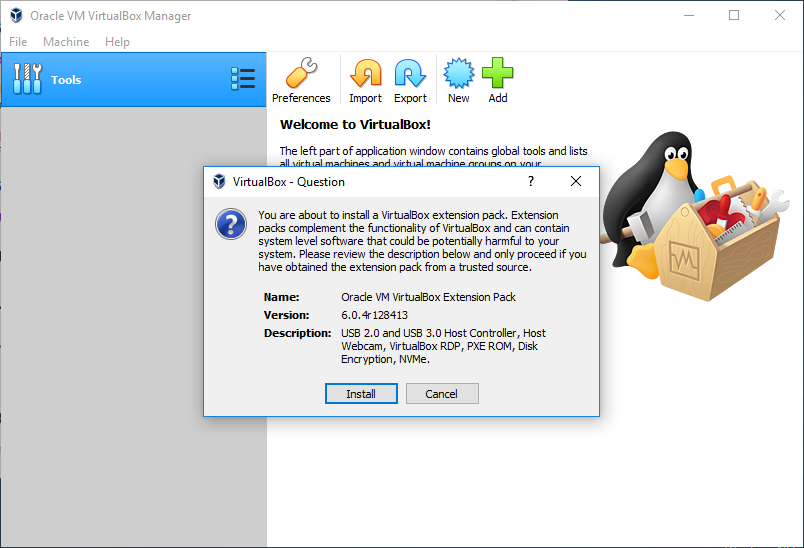
Install the Virtual Box Extensions
In all cases, once the install is completed double click and run the VirtualBox Extensions file you downloaded which will run within VirtualBx and prompt you as follows. Click and install and continue. This will now give you some of the supprot the Kali Linux and other VMs expect and eliminate some of the errors you get when try to use the Kali VM without this extension.
Download & Install the Kali Linux Virtual Machine
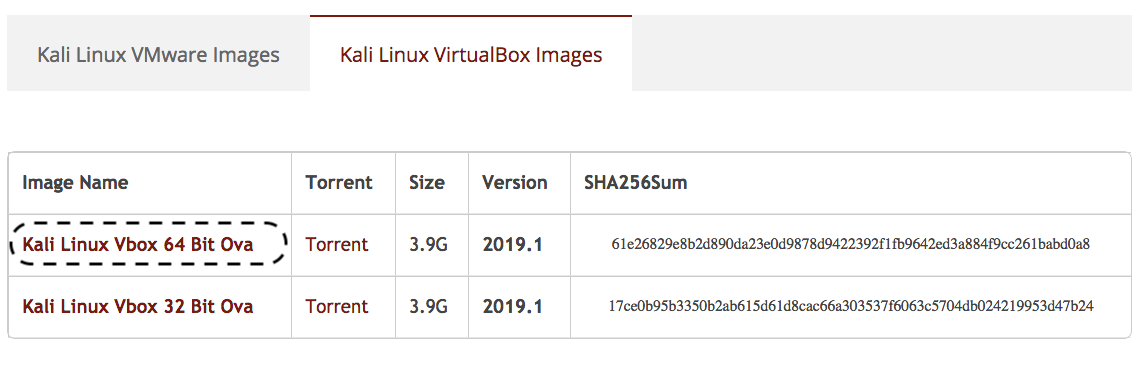
The Kali Linux VMs are available for downloads from https://www.offensive-security.com/kali-linux-vm-vmware-virtualbox-image-download. Make sure you click on the second tab (Kali Linux VirtualBox Images) and click on the 64 bit OVA.
This will download a 4-4GB file with a filename that looks like this kali-linux-<YYYY>.<updateNo>-vbox-amd64.ova e.g. kali-linux-2019.1-vbox-amd64.ova
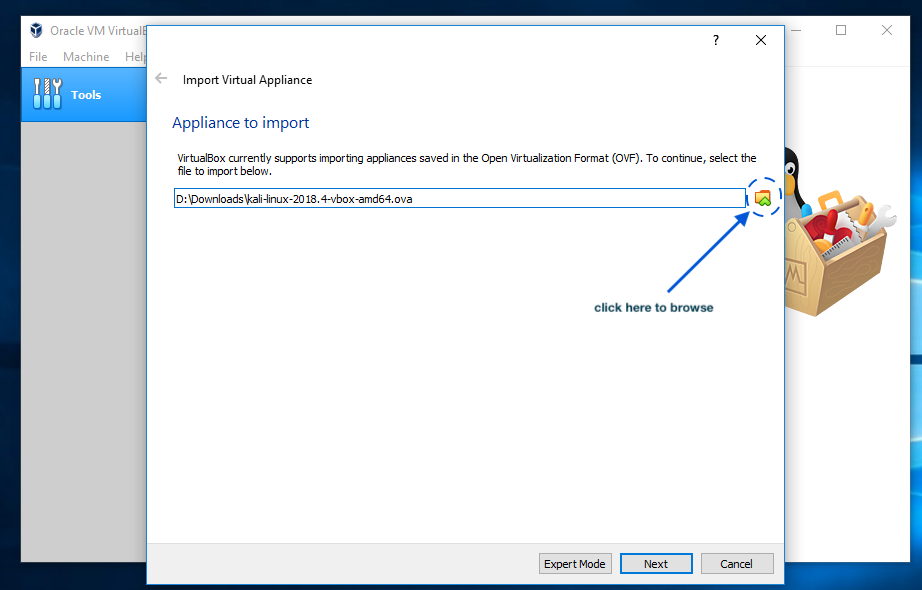
Start VirtualBox and select File, Import, then click on the folder icon to browse and select the Kali OVA file you have just downloaded.
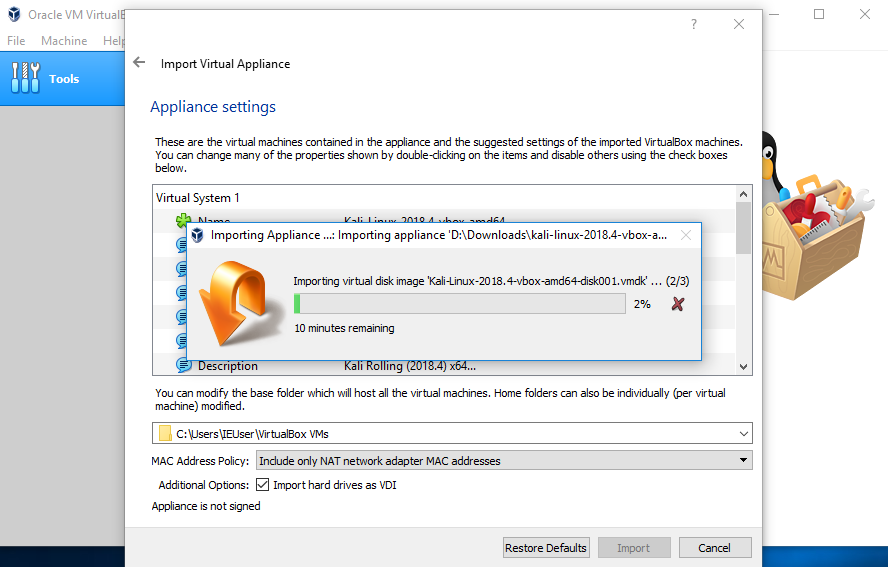
This will take you through a screen with the details of your VM and will then import it creating a new VM. Depening on how powerful your machine is, this will take you about 10 minutes.
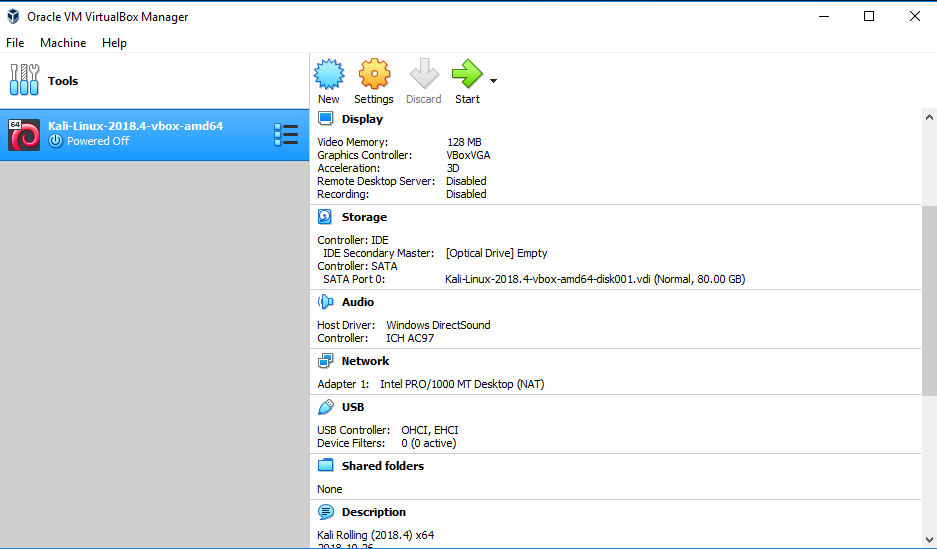
You should now have a new Kali VM in VirtualBox.
But before you can start using it, you need to configure it so that is part of an isolated internal pentest network.
Configure Kali Linux
Networking
Our aim is to create an isolated configuration but have the flexibility to connect the Kali VM to the Internet when needed (e.g. system updates) We will use the Virtual Box’s networking modes to create a Host-Only virtual network as well a NAT connection to the internet, as shown below:
To keep things isolated and safe, we are are using NAT networking instead of Bridged to give Kali access to the external network without giving it an IP address, keeping it inaccessible from your network, outside your computer. On the other hand, we are using Host-Only instead of Internal so that the VMs can access the host (to copy files for instance).
You can learn more about the network types and configurations offered by Virtual Box by reading this section of the products documentation
External Connection
The Kali VM comes with a virtual network adapter configured to use NAT, which will allow you to have an external network connection, so no additional configuration is needed.
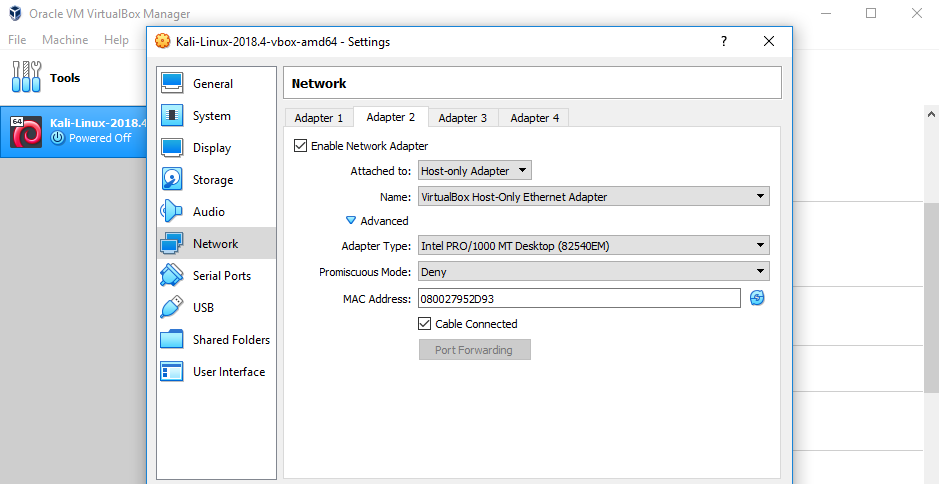
Host-Only Connection
Click on Settings, then select Network, and then Adapter 2
Check the “Enable Network Adapter” checkbox to enable it
In the “Attached to” field select “Host Only Adapter”
Click Ok
You can now start the VM and logon with the user name root and password toor
Download and Install Metasploitable2
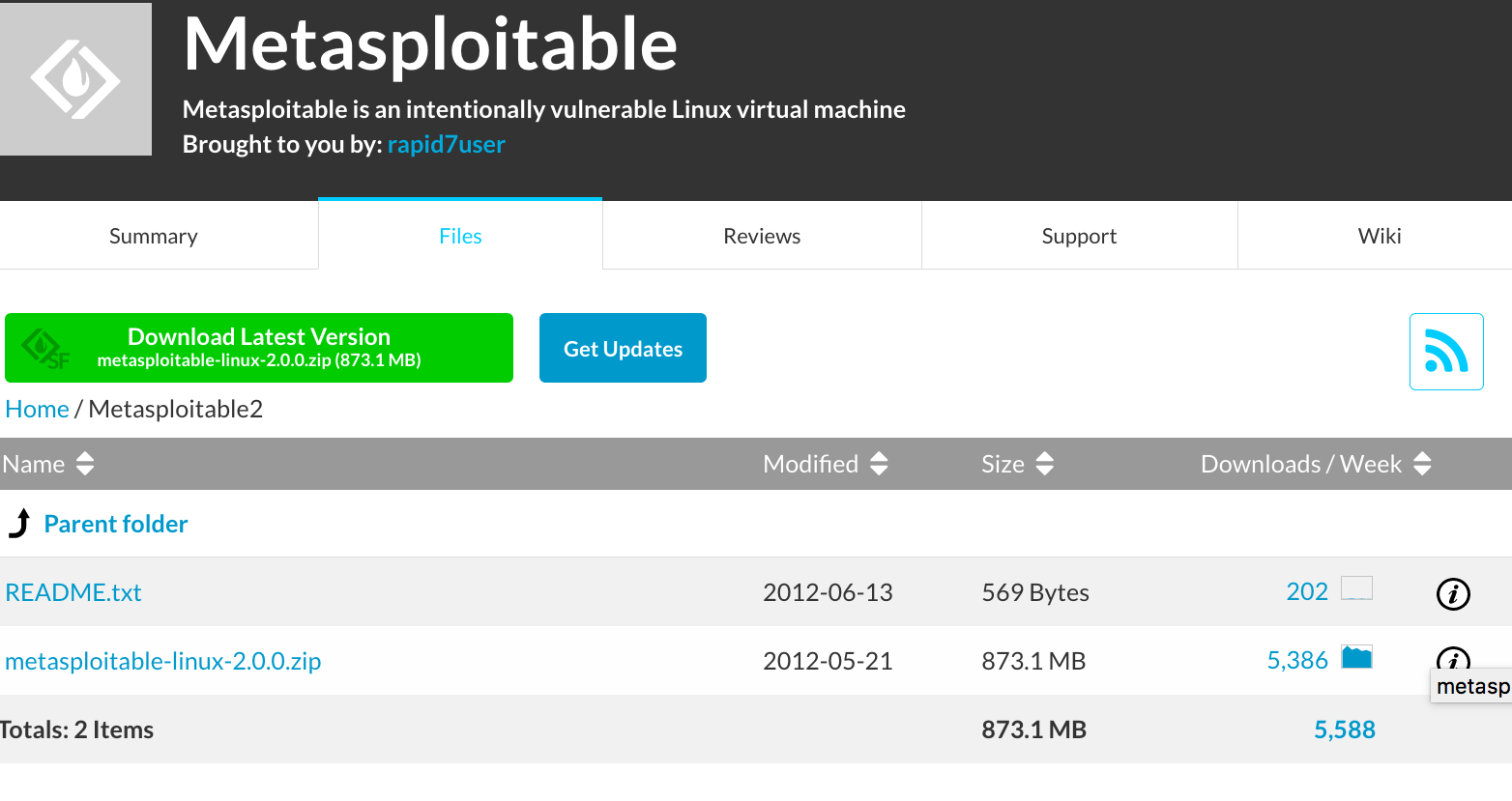
Metasploitable2 is an intentionally vulnerable VM and can be downloaded from https://sourceforge.net/projects/metasploitable/files/Metasploitable2 which brings a page with a Download Latest Version button and a link to the zip file. Click on either and it will dowaload the metasploitable-linux.zip file.
Once downloaded, extract the zip file and you will see a few files. The Metaspoitable2 VM we have downloaded is a VMWare VM and we can use it in VirtualBox by taking advantage of VirtualBox’s ability to use VMWare virtual disks (the ones with the .vxd extension)
From VirtualBox, click New and enter the details as shown in the next screenshot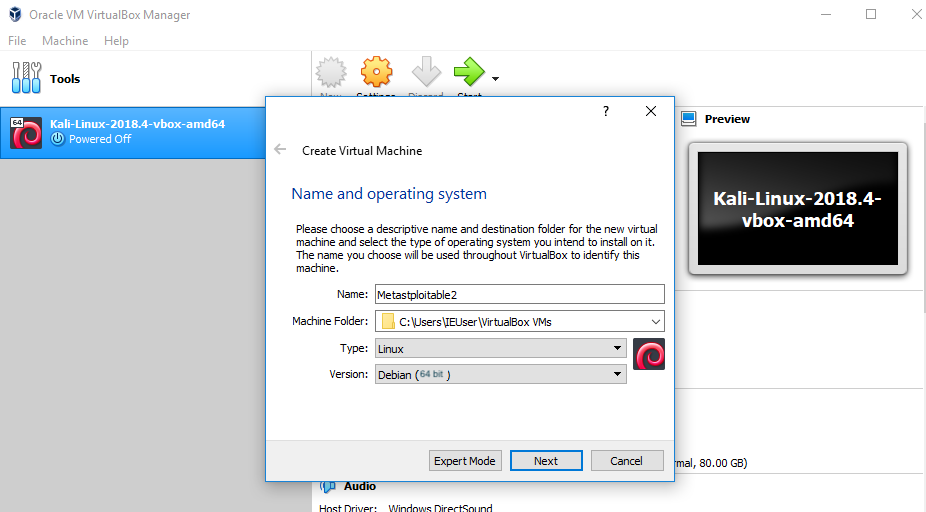
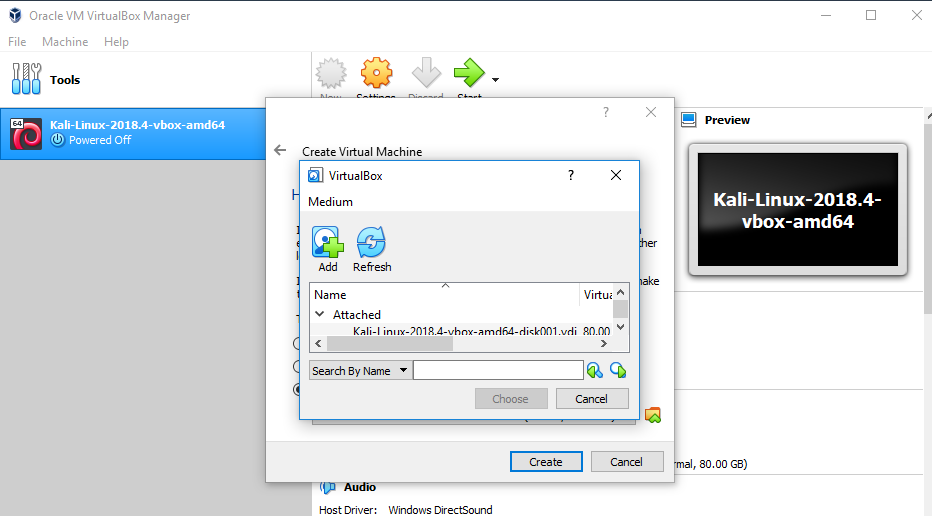
Click Next and then Next again. You will then be shown the dialog box to create or select an existing hard disk.
Chose “Use an existing virtual hard disk” and then click the folder icon next to the drop down. This wil prompt you to add the hard disk
Click Add and browse for the extracted Metasploitable-linux folder. Select the Metasploitable.vmdk file and click OK. Then select the new hard drive and click on the chose button.
Continue to create the new VM and then from settings, configure the new VM Networking by simply chosing “Host-Only Adapter” in the Adapter 1 tab. Click OK to finish.
You can now start the VM. This one only has a command line interface and you can login using the username msfadmin and password msadmin.
Getting Started with your Pentest Lab
The two VMs are now created and you will need to run them at the same time. The Kali Machine will be your pentesting environment whereas the Metasploitable VM will be your safely isolated target.
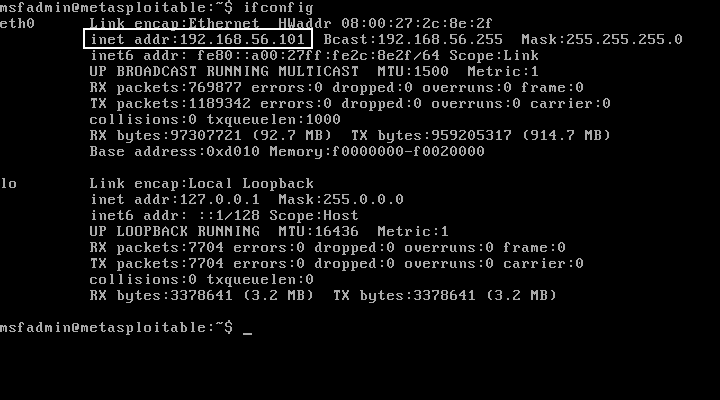
When logged to Metastploitable, type ifconfig and note down the IP address as shown below. This will be the address you will be using as the target IP address in the labs.
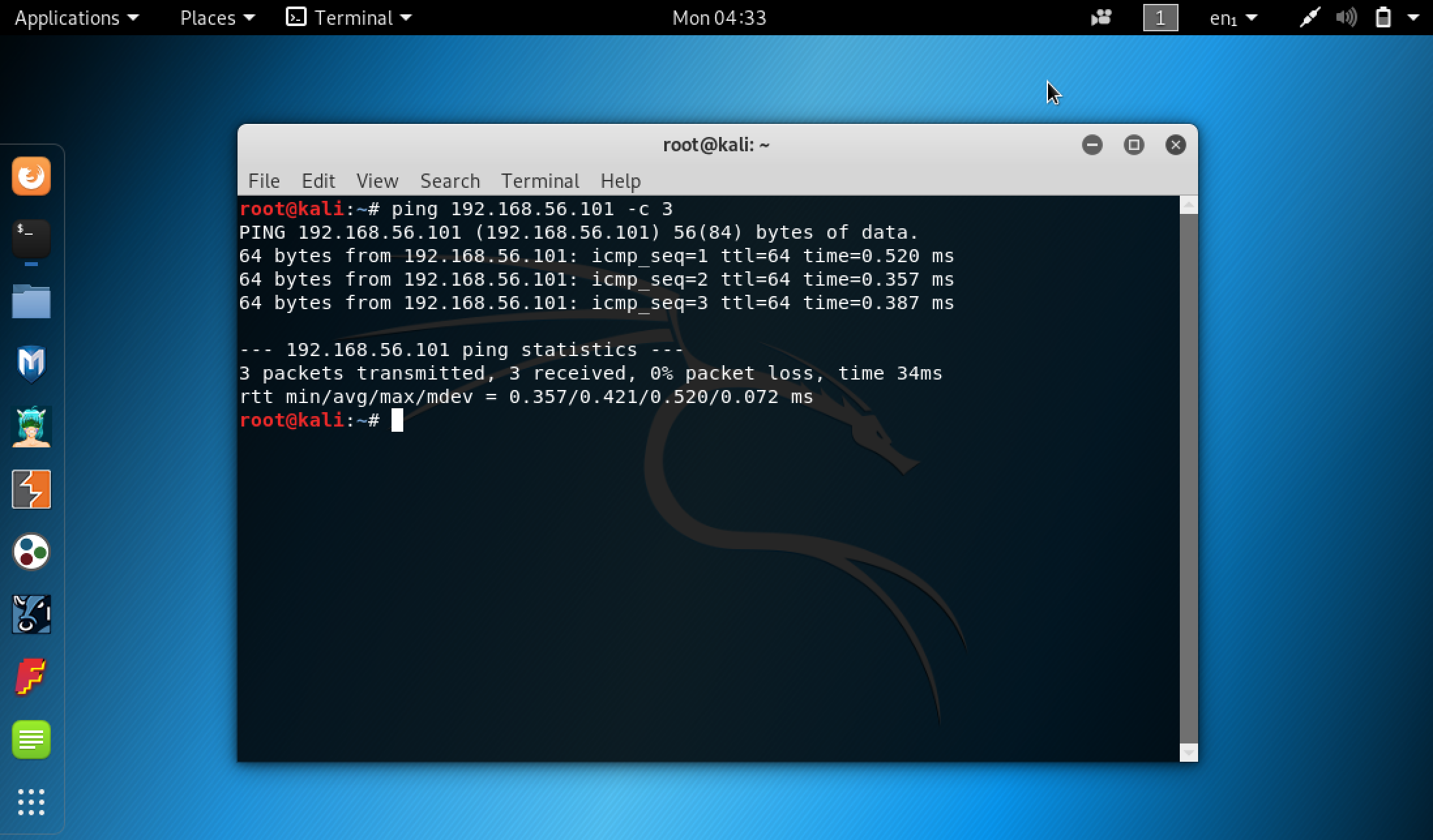
Logon to Kali Linux ( user: root / password: toor) and then click Application / Terminal and from the terminal, type ping <Target IP Address> -c 3 where Target IP Address is the adress you found in the previous step. You should get back 3 responses.
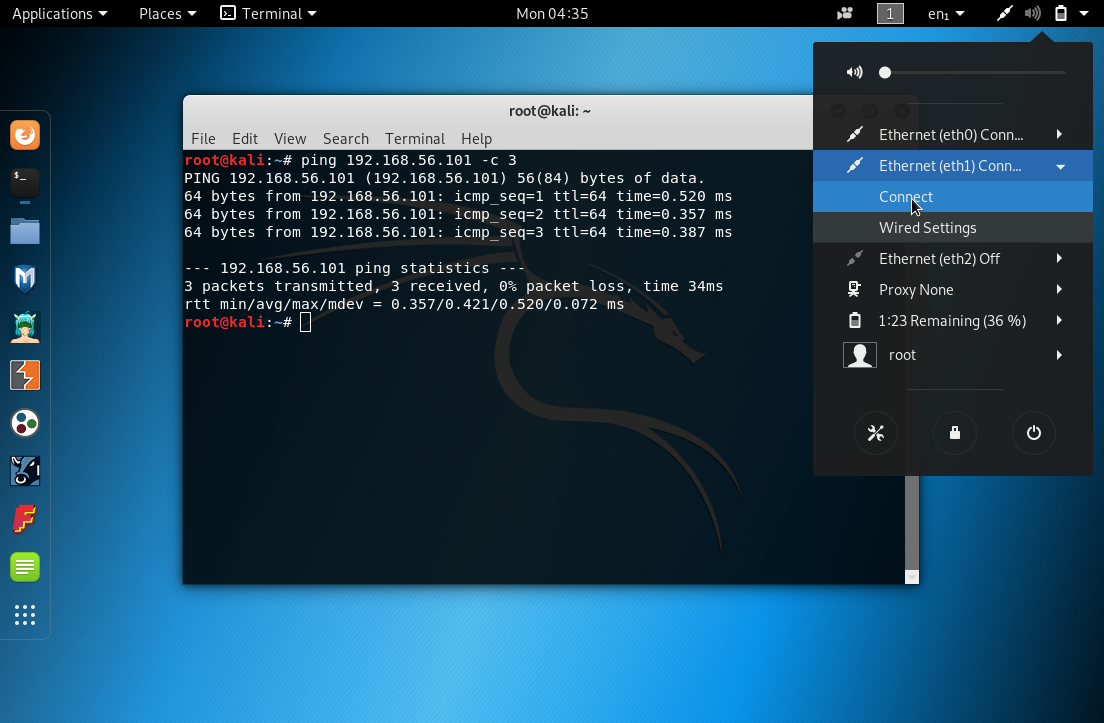
If for some reason, the command times out it will show you results with the “Destination Host Unreachable” message. This means the Host-only network connection is not working. In most cases, it means you need to switch your active connection from NAT to Host-Only. This can be done as shown below, bu clicking on the top rightmost dropdown (settings) and then click on the eth1 entry, expand and then connect. Verify again with a ping command. It should now work. Happy pentesting!
Learning More about your Lab
Before you start using the lab you may want to spend a bit of time on two topics that can help you take most of your pentesting environment and efforts.
Bash Linux Command Prompt
This 13 section tutoirial is a good one to familiarise with the Linux command prompt. Start with the fisrt section and then click next session.
https://ryanstutorials.net/linuxtutorial/commandline.php#bash